CTF Documentation Examples
Overview
Each Product team must have several required documents on file for their CtF application. This document provides examples of these documents.
Plan of Action for [Your Application Name]
- Kick-off Date: MM/DD/YYYY
- Inception Date: MM/DD/YYYY
- MVP Date: MM/DD/YYYY
- CtF Expiration Date: MM/DD/YYYY
Vision
- Describe the overarching vision for your application. This may include benefits the application provides, improvements made to the user's workflow, or where the application intends to go and what you hope to achieve when you get there.
Strategy
- Articulate the mission objectives and expectations that the application aims to achieve. This section may include goals, purpose, or the current and target audience. This section typically aligns with the overall vision and focus of the mission it supports.
Summary
- Provide a brief overall statement and purpose of the application. You may include who uses this application, what it is used for, and when, why, and how it is used.
Goals and Metrics
Release Focus:
- Addition of deconfliction data, notifications, and role-based access
Release Functionality:
- Scheduling of engagement movement between Planned, Staged, and Current states
- Scheduling of events
- Logging of events
- Support for Assessment
System Integration Considerations:
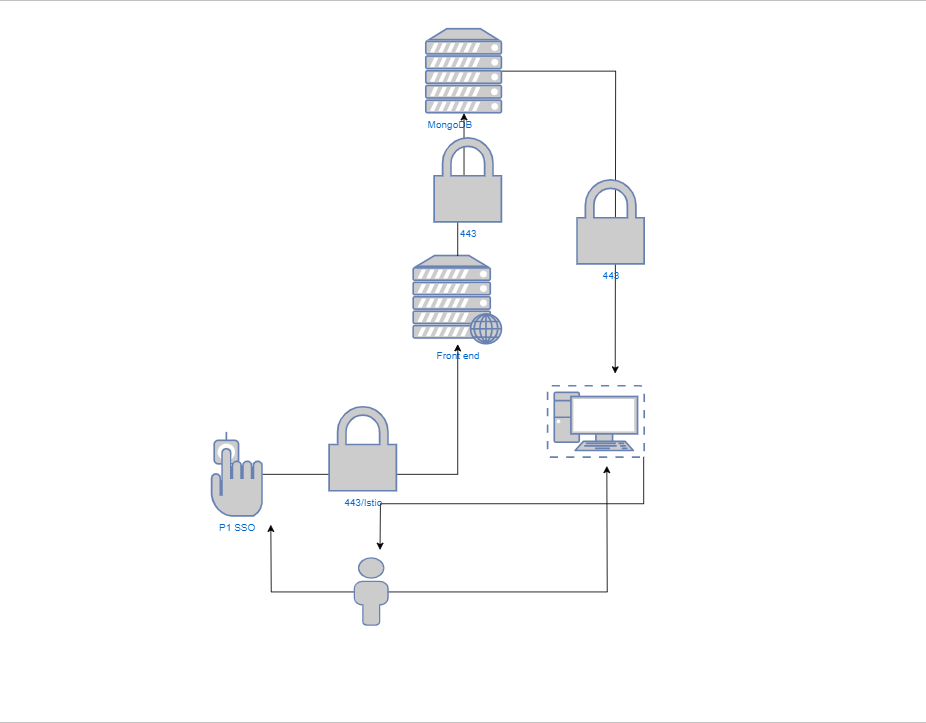
- Interfaces with the MongoDB database
- Interfaces with app assessment and front-end applications as a data access and mutation provider
- Requires access to Keycloak for authentication and authorization
System Security Plan
Complete all bolded items.
Full name of the system.
- System-name: Your Application Name
Shortname or abbreviation.
- Short-name: YAN
Deployment version or release number.
- Version: v4.2.1
Operational Environments: production, test, research and development, tactical, deployed, or other.
- Environment: IL2 Staging, IL4 production
Authorization Status: CtF
- Authorization: Active
List of deployable Pipeline URLs included in CtF.
- Pipeline URLs:
Current CtF Expiration
- Expiration date: date or NA
Security Re-Assess Interval. Period for re-assessment after updates
- Assess-interval: 12 months
Authorization boundary diagram. Include URL.
- System-architecture: https://gitlab.(yourdiagramlink).pdf
Categorization: H/M/L
- Confidentiality: M
- Integrity: M
- Availability: M
Classification:
- UNCLASSIFIED
- SECRET/NOFORN
- TS/SCI
Personally Identifiable Information: Y/N
- PIA: Y/N
- Material Leader's approval:
- DITPR/ITIPS: DITPR/ITIPS Number
- Application team's Program Office maintained: Y/N
Data-types:
- JSON
- HTML
- text
- CSV
Deployment Sites:
Programming Languages:
- React/Typescript
Dependencies:
- Java 11
Databases:
- MongoDB
Platform One External-Systems Hostname:
- Hostname
Role-Identification:
Authorizing-Official:
name: Brian Kropa
title: Authorizing Official
org: Air Force Command & Control
email: brian.kropa@us.af.mil
phone: 781-225-1118
System-Owner:
name: Brian Viola
title: Material Leader
org: AFLCMC/HNCX
email: brian.viola@us.af.mil
phone: 210-421-1458
Chief-Information-Security-Officer:
name:
title: CISO
org:
email:
phone:
Product-Manager:
name:
title:
org:
email:
phone:Architecture Diagram